“New World Pope” = New World Order programming. They designed the “New World Pope” to look contextually small as if to create the illusion of a capstone to this masonic pyramid shaped pose.

The office position of the Pope in Rome is the Biblical, historical and prophetic Anti-Christ.

This January 2014 TIME Magazine cover features the use of occult colors, with emphasis on black, and creates the illusion of red devil horns out of the letter “M”.

Arguably, the most powerful man in the world.

Biblical teachings have to be subverted in order for the upside-down Luciferian New World Order tenets to be universally accepted.

Pope Francis TIME Person of the Year 2013. TIME has him positioned so that it looks like he’s growing horns.
The Catholic church and Pope Francis have been accused of a complicit silence and worse during the “dirty war” of murders and abductions carried out by the junta that ruled Argentina from 1976 to 1983.
The evidence is sketchy and contested. Documents have been destroyed and many of those who were victims or perpetrators have died in the years that followed. The moral argument is clear, but the reality of life at that time put many people in a grey position. It was dangerous at that time to speak out and risk being labelled a subversive. But many, including priests and bishops, did so and subsequently disappeared. Those who stayed silent have subsequently had to live with their consciences — and sometimes the risk of a trial.
Its behavior during that dark period in Argentine history was so unsaintly that in 2000 the Argentine Catholic church itself made a public apology for its failure to take a stand against the generals. “We want to confess before God everything we have done badly,” Argentina’s Episcopal Conference said at that time.In February, a court noted during the sentencing of three former military men to life imprisonment for the killings of two priests that the church hierarchy had “closed its eyes” to the killing of progressive priests.
As head of the Jesuit order from 1973 to 1979, Jorge Bergoglio – as the new pope was known until yesterday – was a member of the hierarchy during the period when the wider Catholic church backed the military government and called for their followers to be patriotic.
Bergoglio twice refused to testify in court about his role as head of the Jesuit order. When he eventually appeared in front of a judge in 2010, he was accused by lawyers of being evasive.
The main charge against Bergoglio involves the kidnapping of two Jesuit priests, Orland Yorio and Francisco Jalics, who were taken by Navy officers in May 1976 and held under inhumane conditions for the missionary work they conducted in the country’s slums, a politically risky activity at the time.
His chief accuser is journalist Horacio Verbitsky, the author of a book on the church called “El Silencio” (“The Silence”), which claims that Bergoglio withdrew his order’s protection from the two priests, effectively giving the military a green light for their abduction.
The claims are based on conversations with Jalics, who was released after his ordeal and later moved to a German monastery.
Bergoglio has called the allegations “slander” and holds that, on the contrary, he moved behind the scenes to save the lives of the two priests and others that he secretly hid from the death squads. In one case, he claims he even gave his identity papers to one dissident who looked like him so that he could flee the country.
For some, that makes him a hero. Other are sceptical. Eduardo de la Serna, co-ordinator of a left-wing group of priests who focus on the plight of the poor, told Radio del Plate that: “Bergoglio is a man of power and he knows how position himself among powerful people. I still have many doubts about his role regarding the Jesuits who went missing under the dictatorship.”Many in the church are keen to move on from that dark period in the history of Argentina and the church. They say the new pope helped to heal the wounds of the dirty war and to restore the credibility of the Catholic hierarchy.
“As archbishop, he faced a monumental task, and he was even accused of collaboration with the dirty war, which he strenuously denied and was ultimately cleared. If he can restore the credibility of the church there [in Argentina], he can handle the scandals that have befallen the church worldwide because he knows how to connect to the people” said Ramon Luzarraga, theologian-in-residence at the University of Dayton.
But the issue is unlikely to go away any time soon, particularly while high-profile trials are still taking place. This week a Buenos Aires court sentenced the “Last Dictator” Reynaldo Bignone to life in jail for crimes relating to the disappearance of 23 people, including two pregnant women, when he was in power in the 1980s. http://www.theguardian.com/world/2013/mar/14/pope-francis-argentina-military-junta

“The Times They Are A-Changin'”. They sure are as Pope Francis is the first Jesuit pope.

In attempting to divine the 78-year-old pope’s comings and goings, the closest Vatican officials have to an intermediary has been Cardinal Pietro Parolin, Francis’s secretary of state, a much respected veteran diplomat—and, importantly, trusted by his boss, according to Wals, “because he’s not too ambitious, and the pope knows that. That’s a fundamental quality for the pope.” At the same time, Francis has drastically reduced the secretary of state’s powers, particularly with respect to the Vatican’s finances. “The problem with this,” Lombardi says, “is that the structure of the curia is no longer clear. The process is ongoing, and what will be at the end, no one knows. The secretary of state is not as centralized, and the pope has many relations that are directed by him alone, without any mediation.”
Valiantly accentuating the upside, the Vatican spokesman adds, “In a sense, this is positive, because in the past there were criticisms that someone had too much power over the pope. They cannot say this is the case now.” http://ngm.nationalgeographic.com/2015/08/vatican/draper-text

Pope Benedict XVI, 19 April 2005 – 28 February 2013

TIME Magazine June 2010. Notice the letter “M” creating the illusion of horns on the top of his Dagon inspired mitre. Besides the fact that this is the only cover where the person is positioned back to the camera, notice the emphasis on the leters “T” and “E”. T.E. sometimes stands for traffic engineering. Considering that it has long been suspected that the Vatican runs the global sex trafficking of children, subliminally this cover is telling us that the Vatican is responsible for traffic engineering.

Benedict was a cerebral scholar who continued to write theological books during his eight years as pope. On this TIIME Magazine cover they are creating the illusion of golden horns on the Pope’s head with the alignment of the “M”.

This cover of Pope Ratzinger features a colonial-looking profile with famous Masonic icons and structures. Notice that the word “ME” appears emphasized and in fact, both the Freemasons and Catholic Church are pagan Babylonian Mystery cults.

This 1978 TIME Magazine cover, “In Search of a Pope” has the illusion of enormous red horns on the unoccupied papal triple crown. The overall effect gives the appearance of a masonic pyramid with the triple crown finishing the capstone. The Papacy calls itself God on earth and king of king and lord of lords. Do the research!

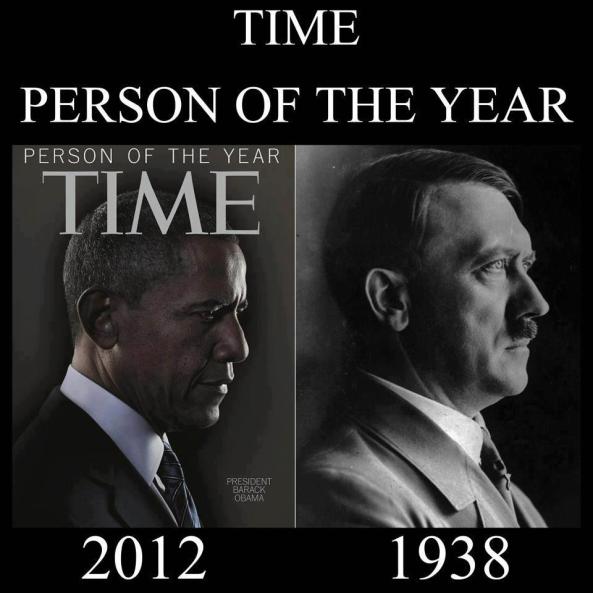
Here’s TIME Magazine’s 1994 Man of the Year before political correctness.

Beloved Pope John Paul II nearly canonized upon death, TIME Magazine chose to not use the “horn effect”.

Pope John Paul II, 16 October 1978 – 2 April 2005

Pope John Paul II

Pope John Paul II was theatrically trained performer and accomplished linguist whose papacy lasted almost 27 years.

1984 John Paul II cover,. It seems that they went way out of their way on this cover to focus of the letter “M”. “M” is for masonry, which was created by the Catholic Church to infiltrate and destroy Protestantism. Freemasonry is run by the Jesuits as are ALL secret societies.

Pope John Paul II cover with the illusion of enormous red horns on his beanie, which called a zucchetto.

Pope John Paul I, 26 August 1978 – 28 September 1978
Pope John Paul I was assassinated after 33 days in office. The precise circumstances attending the discovery of the body of John Paul I “eloquently demonstrate that the Vatican practiced a disinformation campaign.” The Vatican told one lie after another: “Lies about little things, lies about big things. All these lies had but one purpose: to disguise the fact that Albino Luciani, Pope John Paul I, had been assassinated.” Pope Luciani “received the palm of martyrdom because of his convictions.” http://www.tldm.org/News3/JohnPaulI.htm
As the book, In God’s Name attracted worldwide attention, a disinformation campaign arose in 1984 to discredit David Yallop’s conclusions. In a news article quoting Fr. Giovanni Gennari (attempting to defend the Curia against the accusations of investigative journalist David Yallop), Fr. Gennari stated: “John Paul II’s predecessor mistakenly took an overdose of tranquillisers… After his conversation with Cardinal Villot, the Pope [John Paul I] mistook the dose he should have taken.” (Ouest-France, undated press clipping, July 1984) The same article repeats a statement made by Cardinal Villot in 1978, his alibi
Villot: “What occurred was a tragic accident. The Pope had unwittingly taken an overdose of his medicine. If an autopsy was performed it would obviously show this fatal overdose. No one would believe that His Holiness had taken it accidentally. Some would allege suicide, others murder. It was agreed that there would be no autopsy.”
So Cardinal Villot’s alibi was that Pope John Paul I overdosed on his own medication for low blood pressure (Effortil). This alibi intentionally left room for speculation of suicide, to deflect attention away from the real cause of John Paul I’s death: poisoning by Cardinal Villot himself. http://www.tldm.org/News3/JohnPaulI.htm

Pope Paul VI, 21 June 1963 – 6 August 1978
“In Rome and throughout Italy the rumor is out that Paul VI is a homosexual …. When he was Archbishop of Milan, he was caught by the police one night wearing civilian clothes and in not so laudable company. Actually, for many years he has been said to have a special friendship with a red-haired actor. This man did not make any secret of his relationship with the future Pope. The relationship continued and became closer in the years ahead. [After Montini was elected Pope] an official of the Vatican security forces told me that this favorite of Montini was allowed to come and go freely in the pontifical apartments, and that he had often been seen taking the papal elevator at night.”
“The ‘banana peel’ that Paul VI stepped on and that put an end to the confident nature of his weakness was the homily on sexual ethics he delivered in January 1976, dealing with some points on homosexuality. This homily provoked a reaction from the writer Roger Peyrefitte. On April 13, 1976, the weekly Tempo published an interview with this author (with a reputation for very good documentation), … who accused the Pope of being a homosexual and denied his right to be a censor on the topic. Paul VI officially acknowledged the blow.”
“A ‘day of reparation for the offense received by the Pope’ was called for. All of Italy, however, was laughing about the incident. British TV broadcast made an interview with Peyrefitte, who confirmed his accusations and expressed surprise over the publicity he was receiving.”
“The first blackmail against Montini was made as soon as he mounted the steps of the throne of Peter by Freemasonry, which pressured him to do away with the Church’s condemnation of those who ask to be cremated after death (which he did). What it threatened was to reveal the secret meetings between the Archbishop of Milan and ‘his’ actor in a hotel in Sion, in the Valais Canton in Switzerland. In Paris, sometime later, the story behind this change made by Paul VI surfaced, with the indisputable evidence patiently amassed by a gendarme (policeman).” Franco Bellegrandi, Nichitaroncalli – Controvita di un Papa (Rome: Ed. Internazionale di Letteratura e Scienze, 1994. pp. 85-86)
Some pages later, Bellegrandi described what he had personally witnessed. “Another change observed by those in that narrow circle who, because of their position in the Hierarchy or their posts, used to pass a large amount of time inside the Apostolic Palace, was the sudden appointment of homosexuals to positions of prestige and responsibility close to the Papacy. This plague infested, transformed, and devastated the Vatican during the time of Paul VI. It had already begun then [in the pontificate of John XXIII], well hidden in the baroque curtain folds of the Pontifical Court, but, unfortunately, alive and real. But it was the distant hand of the Archbishop of Milan, himself a victim of such weaknesses, that discretely placed one after another on the State chessboard …. the pieces of his game dear to his heart.”
“Those highly situated new personages, who were contaminated by the same ‘sickness,’ naturally brought with them other less highly placed people of the same ilk. Therefore, slowly but continuously, rumors and indiscretions began to flow in the Vatican, and grave facts began to occur as a matter-of-course.”
“Because of their functions, these people were often seen by us [the Noble Guard]. … They also had their favorites, who were the effeminate young men wearing elegant uniforms and make-up on their faces to dissimulate their beards. We (the camarieri di spada e cappa and noble guards) carefully kept our distance from their smiles and courtesies. We limited ourselves to greeting them at distance with the military salute of the heels.”
“‘Favorites’ of the Archbishop of Milan also began to appear at the level of functionary, and both small and large scandals at times would erupt. The Gendarmeria Pontificia [the Vatican police] had to steer carefully .… along those floating mines and keep one eye closed – and sometimes both eyes – to keep reports from leaking and to discourage some sharp journalists …. Honorable old employees who relied on the Governatorato [the administration of the Vatican State] were suddenly fired or removed to other posts, and these newcomers were installed in their empty chairs, all them carrying in their pockets letters of recommendation from Cardinal Montini.”(91-92)
Guimarães ends his chapter by presenting the testimony of Spanish author Pepe Rodrigues, who openly states what would seem to be common knowledge in the inner circles of the European Hierarchy and elites, that there were not only many homosexual Bishops but also a “great homosexual Pope.” (Pepe Rodrigues, “Espana no es diferente,” El Mundo, March 19, 1995, p. 3).
The former claim, at least, can be affirmed without hesitation in face of the continuing crisis of homosexuality the Church is experiencing because of the involvement or complicity of her Prelates with these crimes. The second claim, if true, would explain in part the immense complacency from the highest cupola regarding homosexuality among ecclesiastics.

Confidante of LBJ and fierce supporter of the Vietnam War, Cardinal Francis Spellman. During World War II, Cardinal Spellman undertook a number of missions on behalf of the Papacy, visiting 16 countries in four months.
Cardinal Francis Spellman was the Roman Catholic Archbishop of New York and military vicar of the U.S. armed forces for Roman Catholics. In an address at mass in Saigon, Spellman said that the Vietnamese conflict was “a war for civilization—certainly it is not a war of our seeking. It is a war thrust upon us—we cannot yield to tyranny.” Anything “less than victory is inconceivable.” On December 26, Spellman told U.S. soldiers that they were in Vietnam for the “defense, protection, and salvation not only of our country, but… of civilization itself.” The next day, Vatican sources expressed displeasure with Spellman’s statements in Vietnam. One source said, “The Cardinal did not speak for the Pope or the Church.” The Pope had previously called for negotiations and an end to the war in Vietnam. http://www.history.com/this-day-in-history/francis-cardinal-spellman-visits-south-vietnam
Cardinal Spellman was so involved in the Vietnam War that it earned the nickname, “Spelly’s War”. Spellman was awarded the prestigious Sylvanus Thayer Award by the United States Military Academy at West Point, New York, in 1967. Be not deceived, Cardinal Spellman ran the Vietnam War in America for the Pope in Rome. The Vietnam War was actually a holy war waged by the Catholic Church against the Buddhists in Southeast Asia. https://en.wikipedia.org/wiki/Francis_Spellman
The arch-conservative Spellman was the epitome of the self-loathing, closeted, evil queen, working with his good friend, the closeted gay McCarthy henchman Roy Cohn, to undermine liberalism in America during the 1950s’ communist and homosexual witch hunts. The church has squelched Spellman’s not-so-secret gay life quite successfully, most notably by pressuring The New York Times to don the drag of the censor back in the 1980’s. The Times today may be out front exposing every little nasty detail in the Catholic Church’s abuse scandal, a testament to both the more open discussion of such issues today and the church’s waning power in New York. But not even 20 years ago the Times was covering up Spellman’s sexual secrets many years after his death, clearly fearful of the church’s revenge if the paper didn’t fall in line. (During Spellman’s reign and long afterward, all of New York’s newspapers in fact cowered before the Catholic Church. On Spellman’s orders New York’s department stores (owned largely by Catholics) pulled ads from the then-liberal New York Post in the 1950’s after publisher Dorothy Schiff wrote commentary critical of his right-wing positions; Schiff was forced to back down on her positions). http://www.nypress.com/cardinal-spellmans-dark-legacy/#sthash.tMgSwPYY.dpuf

April 1973 cover of Jesuit Superior General Pedro Arrupe.
Jesuit Superior General Pedro Arrupe arranged for the assassination of Pope John Paul I upon the revelation of the Pope’s intention to disband the Jesuit order and distribute their significant interests, including control of the Vatican Bank to other areas of the church. That Pope John Paul I intended to take this action in part because of the action of the Jesuits in both the assassination of John F. Kennedy, the Vietnam War, the global drug trade as well as Aldo Moro, a national Italian hero. That the murder of Pope John Paul I did prevent the disbanding of the Jesuits from taking place, but did result in a non-Jesuit friendly Pope being elected for the next 27 years.
http://one-evil.org/content/people_20c_arrupe.html
Retired Air Force Colonal Fletcher Prouty, reveals that On Nov. 22, 1963, the government of the United States was taken over by the superpower group that wanted an escalation of the warfare in Indochina, and a continuing military buildup for generations to come.” — JFK: The CIA, Vietnam, and the Plot to Assassinate John F. Kennedy, p. 264.
http://www.pacinst.com/terrorists/chapter8/kennedy.html

Pope John Paul XXIII, 28 October 1958 – 3 June 1963
In 1921, Pope Benedict XV appointed him as the Head of the Holy Inquisition against Heretics for Italy ( Society for the Propagation of the Faith). In 1925 Pope Pius XI appointed him as Apostolic Visitor to Bulgaria. In 1935 he was made Apostolic Delegate to Turkey and Greece. During the first part of World War II, he followed the directives of Pope Pius XII in selling forged papers produced by the Vatican to wealthy families seeking to escape persecution- reaping millions for the church. An unknown number were subsequently captured by the Axis troops.
In 1944 during World War II, Pope Pius XII named him Apostolic Nuncio to Paris, France. In 1953, he was named the Patriarch of Venice, and, accordingly, raised to the rank of cardinal by Pope Pius XII. On October 9, 1958, Pope Pius XII died. Prior to the commencement of the conclave, a number of states including that the Soviet Union had made threats against the election of another hardliner such as Pope Pius XII. The Soviet Union under Khrushchev (1958-1964) on reflection of World War II, Stalin S.J. and the actions of Pius XII was clear that unless a change occurred, he would usher in a new wave of expulsions of the last remaining senior clergy from any Soviet state.
At the Papal Conclave, the conservative fascist Cardinals alliance using their position of strength ignored the threats and elected hardliner Cardinal Giuseppe Siri as the new Pope under the chosen name Pope Gregory XVII. However, at the last minute a small band of Cardinals changed their mind and convinced Siri to step down for a compromise candidate. Cardinal Roncalli was elected on October 28, 1958 as Pope John XXIII- an extremely odd name, given there had been a Pope of the same name several hundred years before, now erased from history. On the 24th July 1959, Pope John XXIII appointed his personal friend Franz Von Papen, the honorary title of secret chamberlain to the Pope. Von Papen was an instrumental and influential figure in the rise of the Nazis and was completely excluded from facing war crimes, in spite of his active involvement. He died on June 3, 1963. http://one-evil.org/content/people_20c_john_xxiii.html

Pope John XXIII, the last picture.

Pope Pius VII, 1953, 2 March 1939 – 9 October 1958
His grandfather, Marcantonio Pacelli, was Under-Secretary in the Papal Ministry of Finances and then Secretary of the Interior under Pope Pius IX from 1851 to 1870 and founded the Vatican’s newspaper, L’Osservatore Romano in 1861;his cousin, Ernesto Pacelli, was a key financial advisor to Pope Leo XIII; his father, Filippo Pacelli, was the dean of the Sacra Rota Romana; and his brother, Francesco Pacelli, became a lay canon lawyer, credited for his role in negotiating the Lateran Treaty in 1929, bringing an end to the Roman Question. At the age of twelve, Eugenio announced his intentions to enter the priesthood instead of becoming a lawyer.
In 1904, Pacelli became a papal chamberlain and in 1905 a domestic prelate.From 1904 until 1916, Father Pacelli assisted Cardinal Pietro Gasparri in his codification of canon law with the Department of Extraordinary Ecclesiastical Affairs. He was also chosen by Pope Leo XIII to deliver condolences on behalf of the Vatican to Edward VII of the United Kingdom after the death of Queen Victoria. In 1908, he served as a Vatican representative on the International Eucharistic Congress in London, where he met Winston Churchill. In 1911, he represented the Holy See at the coronation of King George V
Pacelli became the under-secretary in 1911, adjunct-secretary in 1912 (a position he received under Pope Pius X and retained under Pope Benedict XV) and secretary of the Department of Extraordinary Ecclesiastical Affairs in 1914 — succeeding Gasparri, who was promoted to Cardinal Secretary of State. As secretary, Pacelli concluded a concordat with Serbia four days before Archduke Franz Ferdinand of Austria was assassinated in Sarajevo.
In 1915, he travelled to Vienna to assist Monsignor Scapinelli — the apostolic nuncio to Vienna — in his negotiations with Franz Joseph I of Austria regarding Italy.
Pope Benedict XV appointed Pacelli as papal nuncio to Bavaria on April 23, 1917, consecrating him as titular Bishop of Sardis and immediately elevating him to archbishop in the Sistine Chapel on May 13, 1917.
As there was no nuncio to Prussia or Germany at the time, Pacelli was, for all practical purposes, the nuncio to all of the German Empire. After the war, during the short-lived Bavarian Soviet Republic in 1919 Pacelli was one of the few foreign diplomats to remain in Munich.
Several years after he was appointed Nuncio to Germany, and after completion of a concordat with Bavaria on June 23, 1920, the nunciature was moved to Berlin in 1925. Many of Pacelli’s Munich staff would stay with him for the rest of his life, including his advisor Robert Leiber and Sister Pascalina Lehnert — housekeeper, friend, and adviser to Pacelli for 41 years.
Pacelli was made a cardinal on 16 December 1929 by Pope Pius XI, and within a few months, on 7 February 1930, Pius XI appointed him Cardinal Secretary of State. In 1935, Cardinal Pacelli was named Camerlengo of the Roman Church.
As Cardinal Secretary of State, Pacelli signed concordats with many non-Communist states, including Baden (1932), Austria (1933), Germany (1933), Yugoslavia (1935) and Portugal (1940).
The Lateran treaties with Italy (1929) were concluded before Pacelli became secretary of state. Such concordats allowed the Catholic Church to organize youth groups, make ecclesiastical appointments, run schools, hospitals, and charities, or even conduct religious services. They also ensured that canon law would be recognized within some spheres (e.g. church decrees of nullity in the area of marriage).
Pope Pius XI died on February 10, 1939 and Pacelli was elected Pope Pius XII.
On his election, Pope Pius XII surrounded himself with Jesuits and international clergy, in a break from the traditional Italian control. He employed German and Dutch Jesuit advisors, Robert Leiber, Augustin Bea, and Sebastian Tromp. He also supported the elevation of Americans such as Francis Spellman from a minor to a major role in the Church.
During the Word War II it is noted that Pope Pius XII used the phenomenal forgery skills within the Vatican at his disposal for two famous campaigns- the first being the re-assignment of new identities and papers for thousands of mostly Rabbis and important Jewish officials who – once their “flocks” has been sent to concentration camps somehow magically found their way to Rome.
This work was coordinated with such prominent Zionist leaders such as Chief Rabbi of Rome, Israel Zolli, Chief Rabbi of Jerusalem, Isaac Herzog and Rabbi Safran of Bucharest, Romania who all understood perfectly the Samartian/Sarmatian nature of the Vatican Holocaust.
During this first phase, many of these Rabbi and leading officials who had deeply collaborated with the Nazis were housed not only around Rome, but within the Vatican itself as well as the Papal summer house at Castel Gandolfo. Once their new identities were completed, many then travelling onto Palestine as well as the United States.
The second major campaign coordinated by Pope Pius XII began largely in 1944 with the even greater resources devoted to the forging of new identities for tens of thousands of Officials from Catholic Regimes responsible for mass murder including Nazis, Italians, Romanians, Croatian officials and many of the “Most Wanted” from these regimes.
The Allies names this second phase of the Vatican assistance under Pope Pius XII “the Rat Lines” and many tens of thousand of mass murderers stayed in the very facilities, that a few years prior had housed thousands of Rabbi and Jewish officials.
After the war, Pope Pius XII openly promoted American Catholic clergy above many others such as Joseph P Hurley as regent of the nunciature in Belgrade, Gerald P. O’Hara Nuncio to Rumania and Monsignor Aloisius Joseph Muench as nuncio to Germany.
Pope Pius XII died on October 9, 1958. He was succeeded by Pope John XXIII.
Since his death, there has been a concerted effort by the Vatican and Jesuits to diminish the overwhelming evidence of racial hatred, inaction and evil by this Roman Pontiff, particularly to the Holy Inquisition undertaken during his reign against the Jews.
In the 1960’s, it was the Jesuit sponsored work Three Popes and the Jews (1967), by Panchas. E. Lapide that attempted to portray the grand illusion and claims that Pope Pius XII never met Hitler once, in direct contradiction to the testimony of those closest to Pius for most of his life since Munich and his rise to Pontiff.
Another prominent Jesuit “Jewish” Apologist for Pope Pius XII has been Michael Tagliacozzo who spent nearly nine months under the tuition and protection of the Jesuits at their Gregorian University during World War II and has maintained a steadfast duty to their causes ever since.
In recent years, such authors as David Gil Dail –both a Jewish Rabbi and paid employee and mouthpiece for the Jesuits of Ave Maria University in Florida have achieved considerable positive media coverage for his glowing and saintly portrayal of Pius XII as a savior of “thousands” of Jews in The Pius War (2004), The Myth of Hitler’s Pope (2005).
Most importantly, the verifiable assistance and new identities granted to thousands of Rabbi and Jewish Officials on the orders of Pope Pius XII continues to be presented as one of the most important pieces of evidence as “proof” of his pro-Jewish stance. Rarely, however does any of these historic references reveal the status of many of these individuals as Rabbi and active collaborators with Catholic mass murdering regimes such as the Nazis- explaining how they managed to arrive at the Vatican safely in the first place. http://one-evil.org/content/people_20c_pius_xii.html

Pope Pius XII–Hitler’s pope. This cover has the illusion of a sword through the Pope’s head. Perhaps this was an occult sign that they were going to assassinate the next in line in the succession of popes.
Pope Pius XII is guilty of bribery and extortion for the purpose of extending crimes against humanity (1917) That Pope Benedict XV did commission and authorize Archbishop Pacelli, then papal nuncio (ambassador) also known later as Pope Pius XII, to Munich, Germany in May 1917 under the diplomatic guise to negotiate a Concordat (Treaty) with largely Protestant Germany. That to assist in negotiating such an agreement, the Pope did authorize the release of approximately 60 cases of Gold (over 1,000 gold bars) representing approximately $80 to $100 million (2006 US equivalent dollars) to travel with Archbishop Pacelli under the pretence of “60 cases of special foods for his delicate stomach”. However, these funds, originally themselves obtained through crime were never intended for the support of failing German government and military, but as funds to support anti-Communist political movements and sympathizers.
Pope Pius is guilty of inciting violence and racial hatred (1919-1958) That Archbishop Pacelli later Pope Pius XII did both write, act and behave in a manner of inciting violence, hatred and suppression of rights of individuals upon the basis of their religious, political and ethnic background including, but not restricted to: all black people, all ethnic Jews, all orthodox Christians and communists/socialists.
Archbishop Pacelli, later Pope Pius XII, displayed not only a bitterness towards these groups, but an open hatred and violent anger consistent with their potential demise and/or suppression. In reporting to the Vatican in 1919 concerning the German socialist revolution, Archbishop Pacelli later Pope Pius XII wrote: “An army of employees were dashing to and fro, giving out orders, waving bits of paper, and in the midst of all this, a gang of young women, of dubious appearance, Jews like all the rest of them, hanging around in all the offices with provocative demeanor and suggestive smiles. The boss of this female gang was Levien’s mistress, a young Russian woman, a Jew and a divorcee, who was in charge. And it was to her that the nunciature was obliged to pay homage in order to proceed. This Levien is a young man, about 30 or 35, also Russian and a Jew. Pale, dirty, with vacant eyes, hoarse voice, vulgar, repulsive, with a face that is both intelligent and sly.”
Archbishop Pacelli later Pope Pius XII actively campaigned to have black French troops removed from the Rhineland, convinced that they were “raping women and abusing children” – even though an independent inquiry sponsored by the U.S. Congress, of which Pacelli was aware, proved this allegation false. Pope Pius XII specifically requested the British Foreign Office that no Allied colored troops would be among the small number that might be garrisoned in Rome after the occupation.
Archbishop Pacelli later Pope Pius XII and the Jesuit order under the control of Superior General Wlodimir Ledochowski, helped form the Deutsche Arbeiterpartei (German Workers’ Party), abbreviated DAP, into the National Socialist German Workers’ Party (NSDAP), also known as the Nazi Party as instructed to Adolf Hitler.
The initial purpose of the Nazi Party as formed by the Catholic Church was to:
- Establish a pro-Catholic political party capable of defeating its opposition and gaining control of government
- Establish a Concordant between the Catholic Church and the whole of Germany guaranteeing a massive financial pipeline in compensation for losing the Papal States
- The elimination of all opposition including social reform/democratic minded groups, especially protestants, orthodox christians, communists and ethnic Jews.
Archbishop Pacelli (later Pope Pius XII) mentored Hitler to join the DAP, arranged for him to report to him regularly (at least each month, sometimes weekly) until Pacelli appointment of Vatican Cardinal Secretary of State in 1929 and provided all the financial support and means for Hitler’s rise to Chairman of the NSDAP in 28 July 1921. Furthermore, Archbishop Pacelli used the gold brought in to Germany in 1917 to help fund the rapid expansion of the Nazi Party, including its first reform as a paramilitary organization in 1921.
Archbishop Pacelli (later Pope Pius XII) on instructions from Superior General Wlodimir Ledochowski, instructed Adolf Hitler in 1921 to establish a paramilitary wing to the NSDAP to be known as the Sturmabteilung (SA) also known as Storm Troopers. Jesuit priests trained the first recruits of the SA in espionage, counter intelligence, assassination and propaganda. The purpose of the SA was to assist in the control of organized protests, riots, intimidation of opponents and political assassinations.
the secret agreement by Superior General Wlodimir Ledochowski and later confirmed by Pope Pius Pius XII upon his ascension to the throne, SS officers of the Nazis were given the spiritual powers of Jesuit priests and represented a supreme heresy of Catholic doctrine and faith, against all spiritual teaching. Many of the SS officers were married. Furthermore, by 1939 and upon the power of the Pope, these actions of conferring priestly powers to SS officers active in the Final Solution was in full knowledge of their orders and acts of barbarity and inhumanity. The very purpose of conferring powers of priesthood of SS officers was precisely to make sure that all human sacrifice through the death camps was consistent with the High Mass of Satanism of the Roman Catholic Church.
The Roman Catholic Church of Germany has received and continues to receive payments by the taxpayers of Germany equating to a church tax consistent with the terms of a Concordant signed by Adolf Hitler and Pope Pius XI immediately upon Hitler gaining control of Germany. The historic claim of these taxes date back to Aristocratic tributes to Rome in light of the loss of the Papal States under Napoleon in the 19th Century. These payments to the Vatican have remained intact and have consistently been paid since 1933 before Word War II, during World War II, during the split of Germany and Communism and now under the unification of Germany. These payments constitute the obtaining of property by deception in claiming the Roman Catholic Church to be both an institution of public good and a lawful organization. The total property earned by this criminal organization by stealing from the taxpayers of Germany since 1933 is between $20 and $50 Billion (2006 US equivalent dollars).
The Catholic Church by authority, knowledge and control of Pope Pius XII conspired and received in excess of $10 billion (2006 equivalent US dollars) in payments from the National Socialist Workers Party of Germany, otherwise known as the Nazis, in exchanged for their moral and logistical support concerning the policies of the Nazis towards ethnic cleansing and genocide.
Pope Pius XII with the full knowledge and tacit support of Jesuit Superor-General Wlodimir Ledochowski, handed to the Hitler and Himmler a complete blueprint for the systematic elimination of key non-Catholic minorities across Europe as well as the establishment of death camps for their murder. Furthermore, the Pope instructed that ethnic Jews and other heretics were not simply to be murdered, but ritually sacrificed by being burnt alive, consistent with church law on the penalty of heresy. This plan was to commence immediately and be overseen by the full Jesuit ordained priests of the SS. This plan was called the Final Solution.
As a result of the specific orders by Pope Pius XII, the German command devised an ingenious method of rendering Jews and other heretics unconscious through gas chambers within a matter of a couple of minutes using Zyklon-B. Victims were then restrained unconscious on stretchers and carted to massive furnaces in which they were placed fully alive, whereupon they would awaken screaming as they were burnt alive in the furnace. Contrary to the military fraud perpetrated by Allies commanders loyal to the Vatican, the death camps were established as early as 1940, at least two full years prior to what was claimed at Nuremberg. Furthermore, the camps did not cease sacrificing human beings being burnt alive until 1945. That the single purpose of the death camp ovens was not to dispose of bodies but to specifically burn people alive, consistent with the ancient satanic practices upon which Christianity was first formed by the Sadducee Jewish noble families.
This plan, created by the Vatican, authorized by Pope Pius XII and carried out by full Roman Catholic Priests who oversaw the concentration camps and furnaces represents the single greatest and most evil act of human history to date. Furthermore, the deliberate distortion of facts, the fact that the Pope was never tried as one of the worst mass murderers in history only magnifies the contempt towards international justice and the memory of all those who died. Of crimes against humanity.
Upon the entry of the Nazis into Rome in 1943, the Germans commenced the deportation of over 1,000 Jews who lived near the Vatican. That in a unique gesture, the German ambassador in Rome, fearing an anti-Pope backlash from the general Italian population, pleaded with the Pope on behalf of Adolf Hitler to issue a public protest to at least indicate the existence of some holiness claimed to be possessed by the office of Pope.
No other historical record can be found where Hitler, or any of his officials did grant any person, official or organization the right to criticize it, except for the Vatican. In spite of this unique and extraordinary open invitation by Hitler to criticize him, Pope Pius XII refused and the Jews were sent by cattle cars to Auschwitz for burning. To this day, the Vatican has neither admitted this inhumanity, nor apologized to the 15 survivors.
Pope Pius XII authorized the dedication of significant Vatican resources including finance, the drafting of false documents and secret diplomatic transport of many hundreds of individuals involved in the torture and mass murder of innocent individuals. Some of the individuals saved by the Pope and the Catholic Church included Adolph Eichmann, the supervisor of the extermination of the Jews, Dr Joseph Mengele, the doctor who murdered hundreds of thousands with barbaric experiments as well as senior Croatian officials responsible for the horrendous torture and murder of hundreds of thousands.
The system established by the Vatican to save war criminals from arrest became infamously known as the “Ratlines”. All key personnel of the Vatican had full knowledge of the evil actions of the people it assisted and undertook extraordinary diplomatic risks to ensure the safe passage of the very worst and most evil of the mass murderers. In addition to Pius XII himself, Cardinal Montini (later Pope Paul VI) was in charge of ensuring the successful escape of these individuals.
The Vatican coordinated the transfer of the entire Croatian Ustasha Treasury using allied transport. According to declassified CIA documents, in 1945 the Croatian Treasury consisted of 1700 kilograms of gold, 40,000 kilograms of silver, 2.5 million Swiss francs and a significant amount of diamonds, jewels, and other valuables valued at over $300 million (2006 US equivalent dollars). The treasure was gained through the looting and plundering of valuables from Serbs, Jews, Romani, and citizens of the former Soviet Union, including Ukraine. Only one truck was “allowed” to be stopped and seized with a value of over $30 million in value, while over a dozen other allied transport vehicles deliverd the stolen treasury to the Vatican.
Pope Pius XII personally ensured the safety and escape of Ante Pavelic, head of one of the most brutal and satanic regimes in human history, the Croatian Ustashi. The Catholic Ustashi murdered at least 600,000 people in ways that can only be described as purely satanic including ritualistic cannibalism, crucifixion, live dismemberment, burning alive and excessive torture.
The Pope sheltered Pavelic for a period in Castelgandolfo, the Pope’s summer residence along with other mass murderers and fugitives from justice. The Pope also sheltered Pavelic in the Vatican itself for a period of time. Upon preparing his diplomatic immunity under the Vatican, the Pope arranged for Ante Pavelic to become the aid to Catholic Argentine President Juan Peron. Furthermore, that the Pope ensured virtually the entire war cabinet of the satanist Ustashi successfully escaped.
Pope Pius XII and Jesuit Superior General Jean-Baptiste Janssens, financially supported and lobbied for the election of staunch Catholic President Ngo Dinh Diem as President of South Vietnam in 1955. Upon being elected, the Catholic Church promoted Diem as a Catholic dictator in persecuting Buddhism and all non-catholic interests.
In 1958, the Catholic Church arranged an agreement With Ho Chi Minh that the Catholic Church would not oppose him if he invaded the South and that all money earned from the drug trade would be split more equitably on the condition of protecting French Catholic families and their land holdings managing the opium farms of the Jesuits.
These deliberate actions fermented the conditions for the Vietnam War. Furthermore, upon the commencement of guerilla actions against the South, the Catholic Church through the CIA convinced the American government to support the Catholic South. That upon the election of John F. Kennedy as President, Cardinal Spellman convinced him to escalate the military support of the United States. As a result of these deliberate actions of the Catholic Church, over 2,000,000 men, women and children were killed, including over 50,000 US casualties. http://one-evil.org/content/people_20c_pius_xii.html

Pope Pius XI, 6 February 1922 – 10 February 1939
Pope Pius XI established Vatican Radio in 1931, and was the first Pope to broadcast on radio.
While Pope Pius XI was modern in the use of media as a propaganda tool, the Pope was thoroughly orthodox theologically and had no sympathy with modernist ideas that made fundamental Catholic teachings relevant. He condemned modernism in his writings and addresses.
On the 8th July 1933, the Vatican signed a Concordant with the Nazis regime in Germany. The German representative on behalf of Adolf Hitler was Franz Von Papen.
Politically and morally, the Concordant was unprecedented in its range of concessions. From the date of its signing, all Catholic Bishops and clergy were ordered by the Vatican to pledge an oath of allegiance to Adolf Hitler- effectively turning the entire Catholic apparatus into a state tool of the Nazis (or vice versa).
The agreement also had two immediate effects, the first being that the Nazi Third Reich would pay a significant annual sum to the Vatican in “recognition” for the lost revenues of the Catholic Church since losing the Papal States. In exchange, the Concordant provided the Nazis the highest possibly international credibility as a legitimate government, and not as a temporary holder of power. Thanks in no small part to Pope Pius XI, Adolf Hitler from July 1933 onwards was seen as a legitimate international leader.
This Concordant and the position of Adolf Hitler continues to be honored to this day by the present German Government and every previous government since 1933 in continuing to pay the Vatican what has amounted to Billions of dollars of blood money, tax free. http://one-evil.org/content/people_20c_pius_xi.html
The fascinating background of Adolf Hitler shows his strong lifelong ties to the Vatican and the pope. The Vatican groomed, financed, trained and put Hitler into power to punish the Germans for WWI.
Born in 1889 to devout Catholic parents Alois Hitler and his third wife and niece Klara Pölzl. His father was a Customs Official with some influence and connections, given he obtained a Papal Annulment from Pope Leo XIII of his second marriage in order to marry his half-niece Klara.
The family moved several times during the early childhood years and there are references to the father of Hitler being abusive in the ghost written book Mein Kampf by Bernhardt Staempfle S.J. However, these references contradict the behaviour and open support to Hitler by his parents.
His father had him enrolled at the prestigious Realschule in Linz, where he was in the same class as Ludwig Wittgenstein, the Austrian philosopher who had a profound influence on 20th century logic, mathematics and philosophy of mind; and August Kubizek – who later helped produce two “official” booklets for the Nazi Party on his childhood friend.
A gifted student, Hitler appeared uninterested in study. Following the death of his father in January 1903, he dropped out of high school (Realschule) without finishing his degree.
He moved to Vienna from 1905, in the hope of pursuing a career as an artist, but was twice rejected from the Academy of Fine Arts. In 1907, his mother died from breast cancer and Hitler soon found himself with any family or financial support. By 1910, at the ag of 21, he was living in homeless shelters in Vienna.
In May 1913, Hitler moved to Munich. However, not long after he was arrested for failing to attend for military service. After a physical examination he was deemed unfit for military service and allowed to return to Munich, but upon Germany entering World War I, Hitler petitioned King Ludwig III of Bavaria for permission to serve in a Bavarian Regiment. This request was granted and Adolf Hitler enlisted in the Bavarian army.
During his time in the army, Hitler served as a runner in France and Belgium. he was twice decorated for bravery in 1914 and 1918. On October 15 1918, Hitler was admitted to a field hospital suffering the effects of a mustard gas attack and experience where a British soldier had him at almost point blank range but did not kill him.
After the forces of Germany capitulated at the end of 1918, Hilter remained in the army and returned to Munich. Midst the political chaos of the time, a socialist revolutionary named Kurt Eisner of the Independent Social Democratic Party of germany (USPD) declared Bavaria a “free state” overthrowing the monarchy of the Wittelsbach dynasty which had ruled the region for over 700 years. Eisner then declared formation of the Bavarian Soviet Republic.
Whilst diplomats and wealthy families escaped Munich at the time, newly appointed Papal Nuncio to the region, Archbishop Eugenio Maria Giuseppe Giovanni Pacelli held his ground and was active in the assassination of Eisner on 21st February 1919, and the recuitment and payment of around 9,000 “White Guards” (ex-Germany army) to defeat the Communist forces of around 30,000 under Marinebrigade Ehrhardt.
The role and allegiences of Hitler during these times have been deliberately obscured. It appears, he was initially a supporter of Kurt Eisner having marched in the official funeral procession, but was fervantly anti-communist.
To stop further anarchy or splinter groups by ex-military, the Reichswehr was formed in 1919 and programs instituted to help re-educate former army personnel and identify potentially useful individuals and isolate potential threats.
Hitler attended several of these courses organized by Education and Propaganda Department (Dept Ib/P) of the Bavarian Reichswehr Group, Headquarters 4 under Captain Karl Mayr. It was here that he was singled out as a talented organizer and orator. It is also how he came to the attention of Archbishop Pacelli (later Pope Pius XII).
After being received personally by Archbishop Pacelli, Hitler became one of his protege from mid 1919 onwards, encouraging his promotion within the ranks of the Intelligence Unit of the Bavarian Reichswehr and his mission to infiltrate and report on the activities of the German Workers’ Party (DAP).
From late 1919 until he moved to Berlin in 1925, Hitler would meet with his mentor Pacelli every few weeks and update the Archbishop on the progress of his role and influence. Testimony as a “matter of fact” to the regular and clockwork meetings of Hitler and Pacelli were given by the housekeeper and friend of Pacelli for 41 years, Sister Pascalina Lehnert.
With the influence and direction of the powerful Pacelli, the influence and mission of Hitler changed dramatically from one of low-grade spy to the 55th fully fledged member of the German Workers’ Party (DAP), having been discharged from military intelligence service by March 1920.
In 1921, Pacelli ordered Hitler to convince the party to change its name to the National Socialist German Workers’ Party (NSDAP), also known as the Nazi Party with him as Führer – a role to which he was confirmed on 28 July 1921. Later, the Jesuits wrote the lie in Mein Kampf that this strategic decision to change the party was made by erratic alcoholic and drug addict Dietrich Eckart. What is never mentioned is that Hitler came bearing millions of dollars seemingly out of “thin air” to turn a small eccletic band into a political movement.
Now with his protege in charge, Pacelli pushed for the Nazi Party to accelerate its transformation. Soon after being appointed Führer, Superior General Wlodimir Ledochowski provided Jesuit priests to Adolf Hitler in 1921 to establish a paramilitary wing to the NSDAP to be known as the Sturmabteilung (SA) also known as Storm Troopers first headed by Ernst Röhm.
Using the gold provided by Pacelli, the Nazis secured the first recruits of the SA who were then trained by the Jesuits in espionage, counter intelligence, assassination and propaganda.
In 1923, Hitler was ordered by Pacelli to emulate Mussolini and “march on Berlin” to overthrow the Government, starting with Munich. However, the Nazis were less organized and met stronger opposition than the Italians and never made it out of Munich.
Hitler hid for a time at the home of his Press agent and friend Ernst Hanfstaengl, also a close friend of the Roosevelts and William Randolph Hearst. He was eventually found, arrested, convicted and sent to Lansberg prison for five years.
While at Lansberg, the book Mein Kempf was written for Hitler by Bernhardt Staempfle S.J. with its release coordinated by Ernst Hanfstaengl. He was released in December 1924, having served less than one year of his sentence.
http://one-evil.org/content/people_20c_hitler.html

TIME Magazine cover April 24, 1939 Heinrich Himmler, Germany WWII, Nazi Germany
Born the middle child of three in Munich, Germany to devout Catholics Joseph Gebhard Himmler and Anna Maria Himmler (née Heyder). His father Joseph, was a teacher and principal of the prestigious Wittelsbacher Gymnasium.
Himmler was named after his godfather, Prince Heinrich of Bavaria of the Royal House of Wittelsbach. A gifted student, but socially introspective and poor at sport– a fact that would have deeply upset his father–Instead, young Himmler’s hobbies were chess, stamp collecting, gardening and playing the harpsichord.
Obsessed in the nature of war and politics, Himmler convinced his father to get him into the officer training school in spite of his failure at physical standards for such a role. He graduated within a short period before the end of World War I in 1918 and never saw action.
In 1919, at the age of 19, Himmler decided to become a Jesuit priest enrolling at the Munich Technische Hochschule during the troubles of the brief Bavarian Soviet State and subsequent street battles. It is during this time that Himmler through his influential Catholic family would have come in close contact with Archbishop Pacelli (Pope Pius XII), the Papal Nuncio in Munich.
In 1923, it is alleged that Himmler took part in the failed Beer Hall Putsch but managed to escape arrest. Given his lack of physical strength, it is highly doubtful Himmler was ever one of the Sturmabteilung “Brownshirts” in 1923, but almost certainly an enthusiastic onlooker.
The Sturmabteilung along with the NSDAP were banned as outlaw organizations upon the arrest of Hitler, Hess and the others. While the ban on the NSDAP continued until 1927, incredibly Hitler was released on December 20, 1924 after senior Catholic intervention — having served less than 12 months of the serious (often capital crime) of treason. Of all the great revolutionary leaders of the early-mid 20th century, only Fr Joseph Stalin S.J. is recorded as being so lucky as Hitler with having escaped possible execution and extraordinarily light punishment.
Upon his release, Hitler focused his attention to publicity and the launch of “his” new book Mein Kampf “My Life”. Contrary to deliberate revisionist history, neither the NSDAP, nor the Schutzstaffel (a single German word for “Squadron”) existed until May 1927 –after the ban on the party had been officially lifted. Instead, Hitler was surrounded by a powerful and small group of indivduals each providing key skills such as Rudolf Hess-personal private secretary, Ernst Hanfstaengl-media, Hans Frank-Lawyer and Julius Schreck-personal security.
After graduating as a full Jesuit Priest no later than 1925, there is no precise evidence as to exactly the activities of Himmler until his arrival on the scene in 1929 as deputy of Erhard Heiden.

TIME Magazine February 12, 1945 cover of Heimlich Himmler.
One of (several) absurd mythologies accepted by eminent historians and academics is the proposition that the Schutzstaffel (German for “Squadron” and the same concept as the Italian “Blackshirt Squadrons” of Catholic Mussolini) was formed in 1925 as the personal bodyguard of Hitler following his release from prison.
Some audacious writers have even “revised history” to claim the Schutzstaffel (frequently cut in half to try and get two S’s our of the single word for squadron) had already started to use the SS and skull and bones symbols, including calling their head the Reichführer-SS and the Roman Salute (straight arm) to their allegiance to the Vatican, Rome. The ridiculous nature of these lies are easily exposed when the facts are considered that Hitler’s main claim to fame in 1925 was as a book writer and budding political philosopher.
In fact, the first election of the reformed NDSAP in May 1928 was a complete humiliation and disaster. It was during this period of recrimination and failure that Fr. Heinrich Himmler S.J entered to be immediately appointed the deputy of Erhard Heiden, commanded of the Schutzstaffel (squadron). Within a matter of a few months, Erhard Heiden resigned and Fr. Himmler S.J. was appointed as commander of the Schutzstaffel.
It is a remarkable and rarely considered event occurred- in 1929, a 29 year old rank outsider with dubious military experience, but impeccable Catholic and Jesuit connections is suddenly appointed Reichführer-SS – the 280 most elite security personnel and bodyguards of Hitler himself. There can be absolutely no question that Himmler was a direct Vatican appointment via the support of Jesuits as there is no way Hitler would have accepted such an appointment of such a person into a critical role unless it came from the very highest authority.
Again, it is important to emphasize that the Schutzstaffel (only one S) wore brown shirts until the Reich Concordat was signed between Cardinal Pacelli and Franz von Papen (for Germany) in 1933 bestowing exclusive spiritual powers on the Schutzstaffel of Fr. Himmler S.J. by the Vatican. The Jesuit Skull and Bones was incorporated by Fr Himmler into the military insignia of the Schutzstaffel but not the infamous SS until after the 1933 Concordat.
The political fortunes of the NDSAP appeared to suddenly turn around thanks to the swelling ranks of disciplined recruits to the Schutzstaffel. In September 1930, the NSDAP won 18.3% of the vote and 107 seats in the Reichstag (Parliament). By the July 1932 national elections, this vote had swelled to 37.8% and 230 of the 608 seats of Parliament. However, in the November 1932 elections, their lead had dropped to 33.1% and 196 seats in a 584 seat Parliament. By 1933 National Elections, the Schutzstaffel under the control of Fr. Himmler S.J. numbered at least 52,000 highly trained and absolutely loyal members – a far cry from the early incompetence in Munich ten years earlier. It was March 1933 that the world saw the word “Nazi” unleashed as a political religious force in the elections following the destruction of the Reichstag (Parliament) by Schutzstaffel agents and blamed on communists.
To distract as much as possible from the Jesuit connections, soft history was created in the form of allegations he married or was in a defacto relationship with an already pregnant Protestant woman seven years his senior called Margarete. A convenient window dressing rarely challenged in spite of the fact Himmler was famously known for being a devout Catholic from a devout and powerful Catholic family. In another brilliant misdirection, some rare claims exist stating that Himmler had an “uncle” who was a Jesuit priest and that any reference to Fr Himmler S.J. is the uncle, not Heinrich.
There is a parallel and quite extraordinary change within the power structure of the NSDAP as the Nazis–the rise of Fr. Himmler to Reichführer (also Reichführer Nazi SS) – or Superior General of the Knights of the Holy See–SS standing for Sedes Sacrorum or “Holy See” in Latin.
Many historians deliberately mask the first beginnings of the use of the title Reichführer by dropping off the word “Nazi”, or removing “SS” to somehow claim this position was the official title of the commander of the Schutzstaffel as early as 1925. The reason for this forgery is twofold- one to mask the true date of 1933 as the historic shift in the introduction of the initials SS and secondly to mask the true arrival of Himmler in 1929 and the title Reichführer-Nazi SS in 1933.
But what is more incredible is the fabricated history that continues to hide the absolute fact that in 1933 after the Reich Concordat was signed with the Vatican, Fr. Himmler was elevated in power, name and status above Hitler. Fr. Himmler S.J. as the Reichführer, has a superior title (as opposed to plain old führer for Hitler). Fr Himmler had complete independent control over all police, paramilitary, intelligence, scientific research and weapons development and the dreaded elite units of over 50,000 just in 1933—and Hitler had absolutely no authority over him. In fact, the proof of the distaste each man had for one another is demonstrated in countless war archive movies showing in clear detail the body language of both men.
Prior to its use by Himmler, the symbols SS were most frequently and officially used as the abbreviation of Sedes Sacrorum or the legal name of the Vatican being the “Holy See” (Latin Sedes = seat/see and Sacrorum = Holy/Sacred) since the 16th Century as a sign of imprimatur over official Vatican documents.
It is either an extraordinary coincidence that Himmler and his elite began wearing the SS symbol as Reichführer immediately after the signing of the Reich Concordat in 1933 with the SS- the Sedes Sacrorum, the Holy See. Given the four hundred year precedent of SS being associated with the Holy See, it is not unreasonable to conclude that the wearing of the symbols is associated with some as yet unpublished spiritual/temporal powers bestowed on the SS Troops by the SS- Holy See.
When one considers that Nazi SS translates most perfectly into the meaning “Knights of the Holy See”, that the role of Himmler best translates into the new Grand Inquisitor and that over 18 million innocent people were burned alive in human sacrifice camps in Poland and Russia, then the SS were without doubt the new “Holy Army” of a great inquisition against “heretics” orchestrated by the Vatican, Rome.
The fact that Hitler could do nothing against Himmler at the end of the war when it is universally recognized that Himmler was seeking to broker some kind of personal peace deal is more than enough evidence to conclude Hitler was part-puppet to larger forces.
Finally, the fact that neither Hitler nor any of his henchmen ever attempted to assassinate Himmler, in spite of his open usurping of Hitler’s authority on many occasions, is indication the title of Reichführer-Nazi SS and the meaning of the SS is extremely significant.
In 1934, Himmler successfully convinced Hermann Göring, and General Werner von Blomberg that Ernst Röhm and others were plotting against the Nazi Party. Röhm and several others were murdered in what became known as the Night of the Long Knives on 30 June 1934. The next day, the SS became its own independent organization. In the same year, Himmler was named head of the Gestapo, the German secret police. In 1936, Himmler was appointed Chief of the German Police.
On February 10, 1939, Archbishop Pacelli was elected as Pope Pius XII. Himmler headed the delegation of Nazis who traveled to the Vatican to congratulate their patron. It was in Rome in February 1939, that Himmler first received his instructions concerning the Grand-Counter-Reformation Strategy- the single largest crusade by the Catholic Church to end the hold of Protestant states once and for all, coupled with a plan to remake the Middle East.
But the most extraordinary nature of this event with Pope Pius XII and Fr Himmler S.J. has never been properly realized–for in 1939, Pope Pius XII called into action Himmler as Grand Inquisitor of the Holy Inquisition — to eliminate heretics and usher in a new era of Catholic power throughout Europe.
At the meeting, Pope Pius XII with Jesuit General Ledóchowski outlined his strategy to the key Nazis. Enemy no 1, were Protestants intellectuals. The wedge strategy were the Jews. Jesuit Himmler knew that since the days of Martin Luther who made a fortune selling anti-Jewish pamphlets, the Protestants of Europe had shown a fierce anti-semetism towards the Jews. Now this anti-semitism would be used for their downfall.
Within weeks of securing Poland, Himmler rallied substantial resources to commence building the human sacrifice camps as instructed by Pope Pius XII and the Catholic Church in Rome. The centerpiece was the ovens, in which millions were to be sacrificed to Moloch, the ancient demon god of the Sadducee High Priests. The gas chambers were designed to render victims unconscious, allowing their securing on metal trays for the furnaces easier. Contrary to falsified documents and testimony, the camps began operation by 1940, not ending until 1945.
Himmler personally toured the camps and the selection of staff, in which Jesuit priests, including Franciscans were embedded within the SS and were placed in rotation to pray satanic prayers in front of the ovens so that at all times, the burning and dying were being properly cursed. Musicians were even employed from the prisoners to drown out the screams of the people being burnt alive in the ovens.
In 1944, Himmler became Commander in Chief of the newly formed Army Group Upper Rhine to fight against the US 7th Army and French 1st Army. However, he failed to show leadership in the field capabilities and by March 13th 1945 abandoned his command claiming illness.
In late March 1945 Himmler then started negotiations with Count Folke Bernadotte of Sweden at Lübeck to contact the Americans and British on how a peace settlement could be secured, however, his negotiations failed. Considering the extreme punishment given to failing generals in the last years of the Third Reich, the actions of Himmler testify to him being virtually untouchable, even by Hitler himself. Undeterred, Himmler then allegedly contacted the headquarters of General Dwight D. Eisenhower the details of which remain shrouded in mystery and contradictions.
Yet more controvesy in a life of controversy concerns the events surrounding the capture and alleged suicide of Himmler. On May 22 1945, Himmler was “found” by a British unit. But it is alleged he managed to commit suicide the following day by swallowing poison before being interrogated.
After being alerted that Himmler had been found, Allied Command ordered an official autopsy be conducted, including photographic and forensic evidence–an extremely rare event during wartime. But for all the care allegedly carried out on orders of the Allied command concerning the “dead” Himmler, the next fact defies all logic and reason–his body was then supposed to have been quickly buried in an unmarked grave with deliberate attempts to hide the precise location. To this day, the exact site is not known. While historians claim this is not a big issue, it remains one of the greatest contradictions and absurdities of history.
Given the extraordinary and contradictory allegations that the body of Himmler had been disposed and hidden so quickly, the alleged autopsy records and a few choice photographs were all that remained as verification of his suicide- except the fact that the autopsy apparently failed to record a number of key and unique distinguishing features of Himmler- the most obvious of which was a scar on his face since childhood.
When put together with the events of Himmler openly seeking safe passage prior to his capture and the extraordinary events around his alleged death, it is almost certain Himmler was secretly relocated.
Again, contrary to revisionist historians who perversely on the one hand try to play up the power of Himmler and on the other down-play his intelligence value to the Allies– particularly being in charge of every single Nazi scientific and military project. Himmler would almost certainly have been The Great Prize for the United States in terms of knowing the key scientists of weapons research, rockets and advanced aircraft. The only problem would have been to have Fr Himmler in a location close enough to mainland United States, but under a regime that would ensure his identity would not be exposed–Cuba.
Contrary to the deliberate falsity that Argentina was the largest population of Nazi war criminals outside US military bases after World War II, Cuba remained a key haven for prestige former Nazi officials such as Fr Himmler, in spite of the political turmoil. In reality, the Jesuits continued to rule the island nation with an iron fist and the return of Fulgencio Batista in 1952 only strengthened their hand.
Upon the death of his life long mentor and friend Pope Pius XII on October 9, 1958, Fr Himmler S.J. probably died soon after. Soon after the death of Fr Himmler, the forces of Jesuit trained Castro launched their offensive to “takeover” Cuba and get rid of those in power with knowledge. By January 1, 1959, the most senior military and intelligence officials of the former regimes were arrested and executed. executed. http://oneevil.org/content/people_20c_himmler.html
“Ye shall know the truth, and the truth shall make you free” (John 8:32, KJV). But to find the truth, one must study the history of the Roman Catholic Church and the Jesuits.